About 80% Vulnerable?
Four researches, Yossef Oren, Vasileios Kemerlis, Simha Sethumadhavan, and Angelos Keromytis, wrote a paper on how an attacker could monitor someone by CPU Cache.
Modern personal computers use a virtual memory mechanism, in which user processes do not typically have direct knowledge or access to the system’s physical memory. Instead, these processes are allocated virtual memory pages. When a virtual memory page is accessed by a currently executing process, the operating system dynamically associates the page with a page frame in physical memory. The CPU’s memory management unit (MMU) is in charge of mapping between the virtual memory accesses made by different processes and accesses to physical memory. The size of pages and page frames in most Intel processors is typically set to 4KB,
and both pages and page frames are page aligned – the starting address of each page is a multiple of the page size. This means that the lower 12 bits of any virtual address and its corresponding virtual address are generally identical, another fact we use in our attack, researches noted.
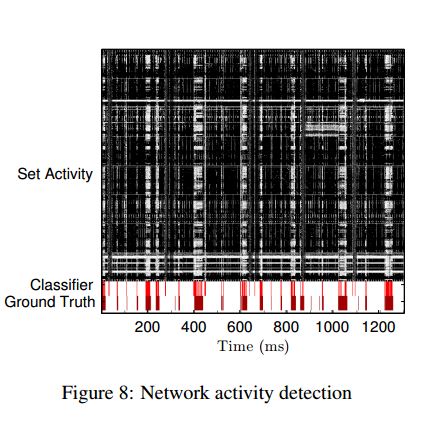
Once the malicious JavaScript is running, it primes the cache into a known state, waits for the user to do something like press a key, and then uses the browser’s high-resolution timer to record the time it takes to iterate through a block of memory; when accesses are considerably faster than others, the memory being touched is still in the cache. With that information, the attacker can map the pattern of memory accesses to keystrokes and mouse movements, which can be replayed
The cache attack is the most well-known representative of the general class of micro-architectural attacks
On Intel Core i7 Mac running OS X 10.10.2 and Firefox 35.0.1, the JS was able to map half the L3 cache in one minute, and about a quarter in roughly 30 seconds.
Countermeasures?
In the meantime the best suggestion I have for end-users is: close all non-essential browser tabs when you’re doing something sensitive on your computer.
The attacks described in this report are possible because of a confluence of design and implementation decisions starting at the micro-architectural level and ending at the Javascript runtime: The method of mapping a physical memory address to cache set; the inclusive cache microarchitecture; Javascript’s high-speed memory access and high-resolution timer; and finally, javascript’s permission model. Mitigation steps can be applied at each of these junctions, but each will impose a drawback on the benign uses of the system